Doug Mohoney at FierceTelecom reported this incredible (too strange to be true) story about abuse of public safety resources. Called…
Read MoreBroadcast SMS as Public Safety Service
The first report of Brockmann & Company, First Communications was on public safety and business users' recommendations. In the research,…
Read More
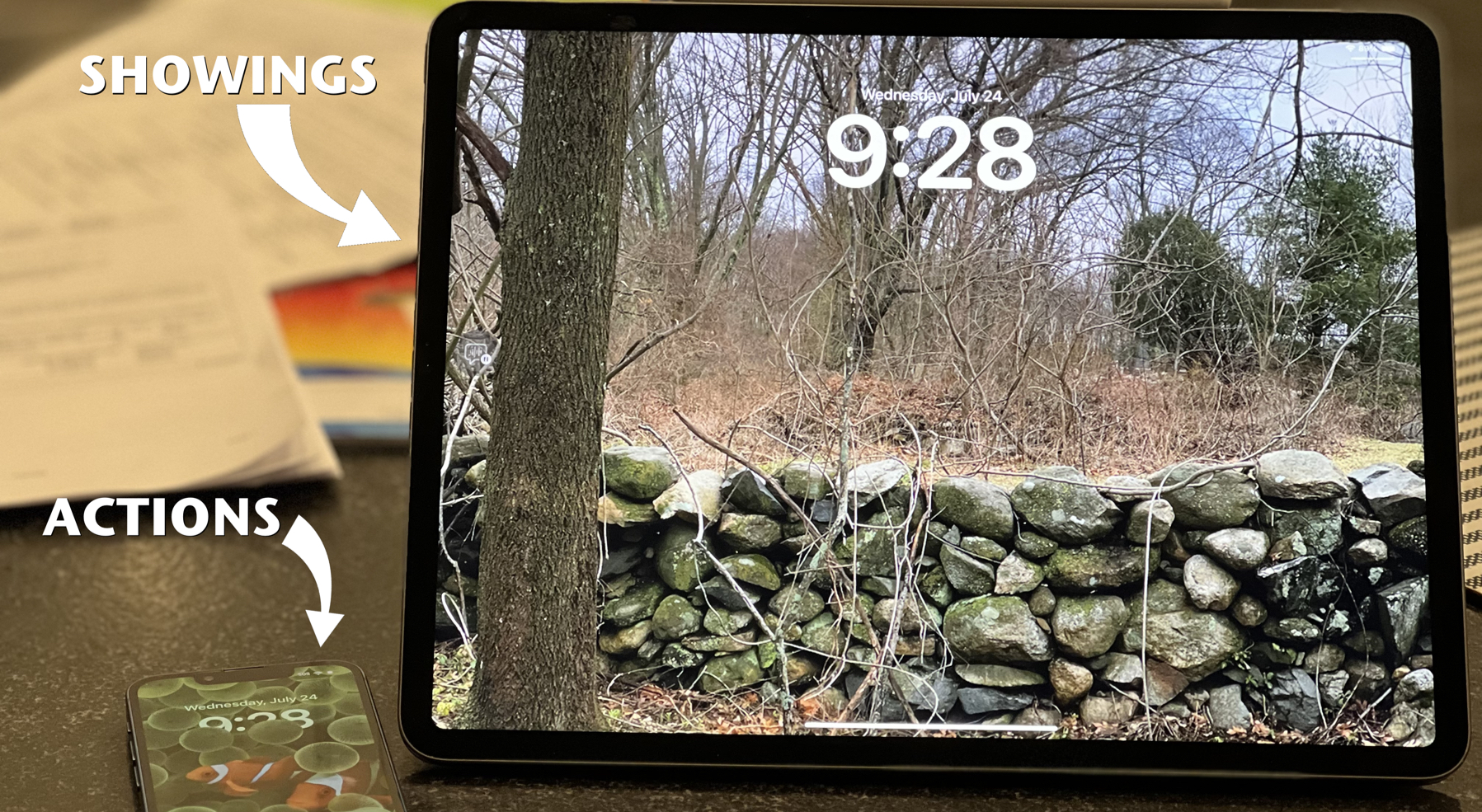
eTelemetry Associates Traffic Sources with People
While tooling around central MA on my little red motorcycle earlier last week, I came across two motorcycle enthusiasts (until…
Read MoreJames Kim Dies After Leaving Car & Family
Sadly, it's a story of one mistake, one death and one great technology. James Kim, a C|Net editor, with a…
Read MoreAIM PhoneLine Supports E911
Using a technique I proposed in November 2004, AIM solves this demanding issue. Having users confirm the physical address of…
Read More