Probably not part of Samsungs advertising budget of several billion dollars last year, is the fact that their devices are…
Read MoreIdentity Thieves Masquerade as Job Sites
The creation of job posting websites like monster.com, hotjobs.com, careerbuilder.com or even dice.com has really made the marketplace of employers…
Read More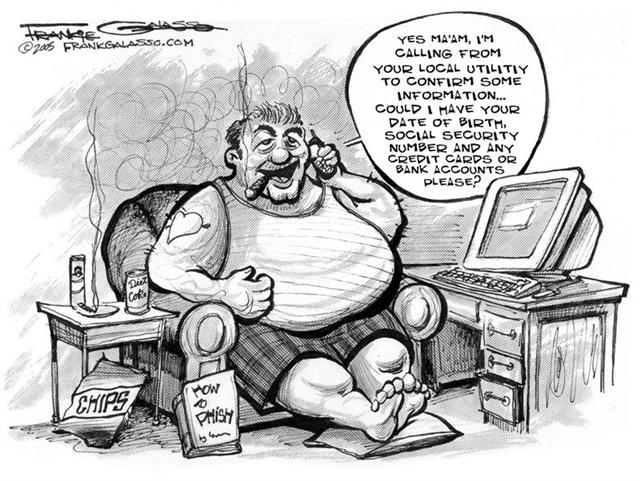
Identity Theft Getting Easier
Identity theft is a $50 billion problem, and the habits of citizens can sometimes make them targets for identity theft.…
Read More
NCP Introduces Server to USA
Some folks think that recessions are exactly the wrong time to introduce new products. Sadly, these industry laggards miss out…
Read More
Lawful Intercept Focuses on Skype
In a nod towards lawful EU intercept of Skype calls, Skype earns endorsement from an Italian drug dealer. The Luxemburg…
Read More